UNESCO's Publicly Accessible xmlrpc.php File
United Nations Educational, Scientific and Cultural Organization (UNESCO)
My first attempt at reporting a vulnerability to UNESCO in October 2025 was unsuccessful. I remember spending weeks manually auditing their subdomains after discovering their vulnerability disclosure program. Looking back, my lack of experience was likely the main obstacle.
My general strategy for new responsible disclosure programs is simple: once I find an initial vulnerability, I email the organization and gauge their responsiveness. I then adjust my approach based on the complexity of the target and how quickly the team communicates. If the effort required to reach the Hall of Fame seems disproportionate, I either aim for a single submission or move on to a different program and return later.
In January 2026, I decided to try again. After studying write-ups from other ethical hackers and reviewing previous vulnerabilities in UNESCO's Hall of Fame, I increased my efforts. I specifically targeted the XML-RPC endpoint. While I knew others had reported this in the past, I wanted to see if any instances remained.
Using the Wappalyzer extension, I screened UNESCO's enumerated subdomains. For every site running WordPress, I manually appended /xmlrpc.php to the URL. Eventually, I found a live endpoint.
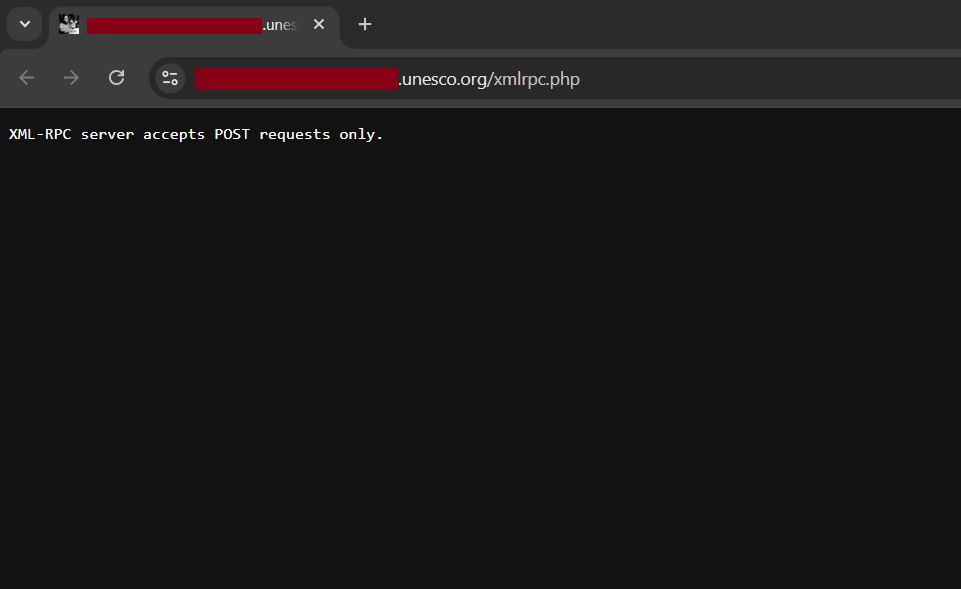
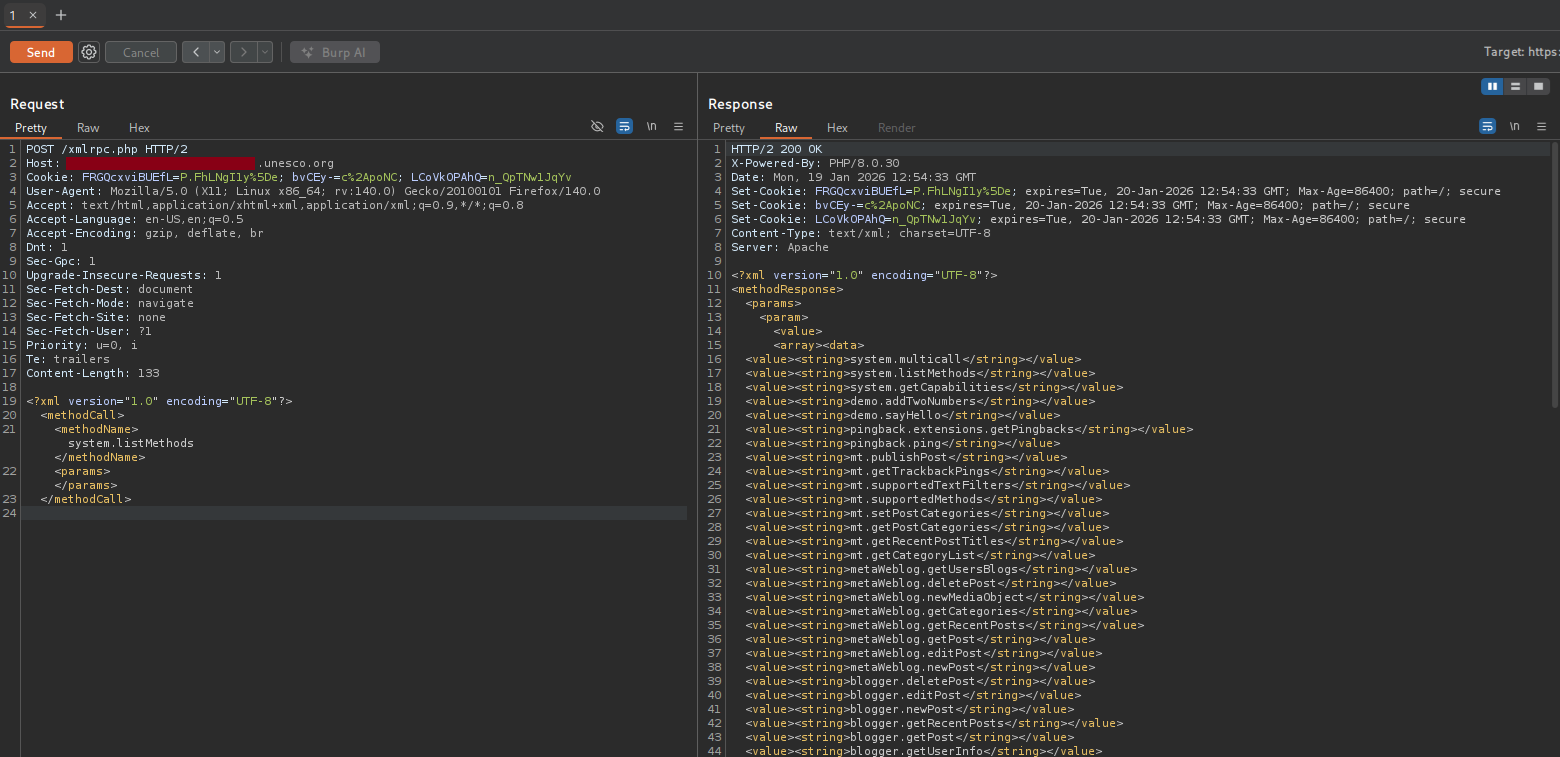
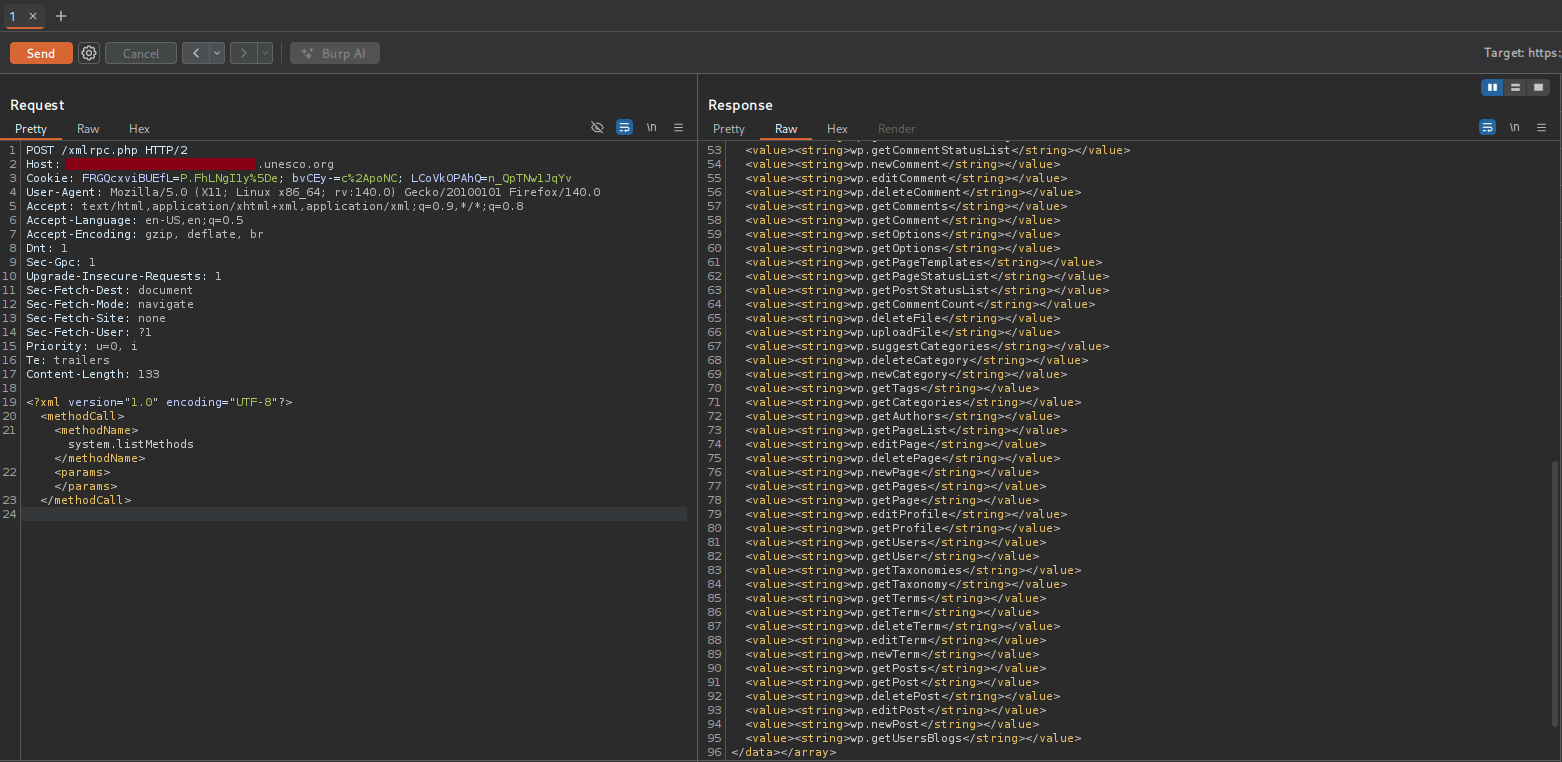
To rule out a false positive, I used Burp Suite to intercept the request.
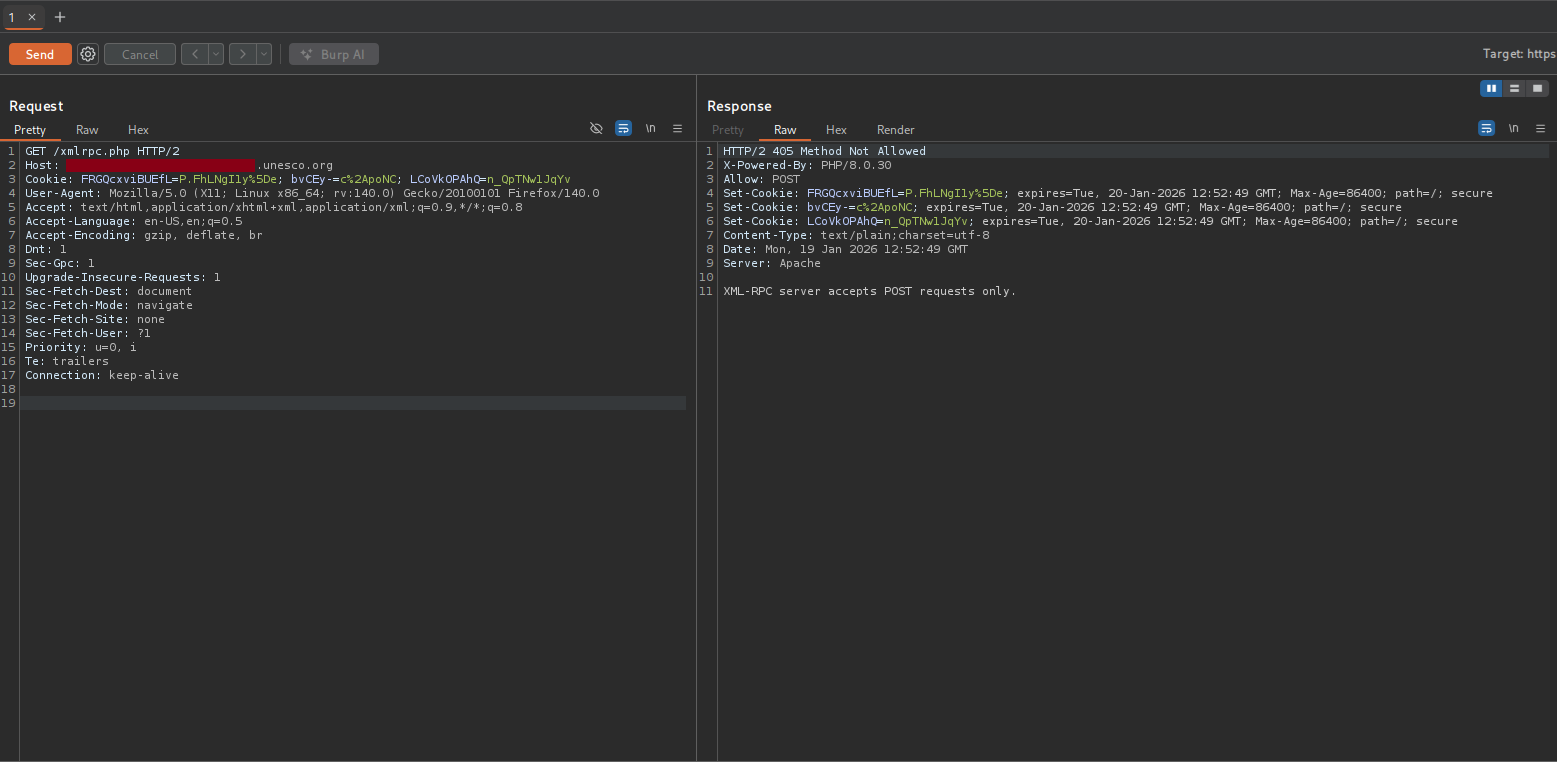
I changed the request method from GET to POST and successfully listed the available system methods.
Since this was sufficient proof of the vulnerability, I submitted my report to UNESCO's Digital Security team on 19 January 2026. After waiting a few weeks, I received a reply on 11 March 2026 confirming they had accepted and fixed the issue.
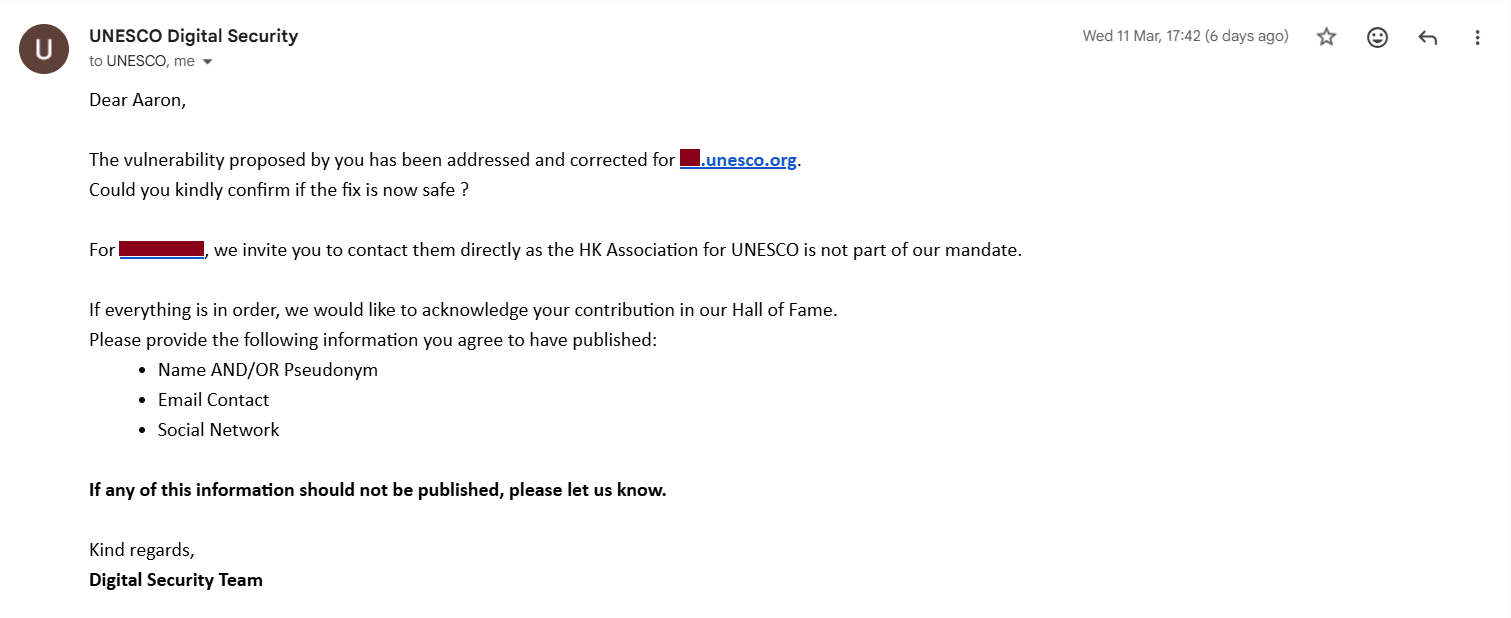
That's nice! So they accepted this small vulnerability and fixed it. I manually verified the fix and provided the team with the necessary details for my listing.
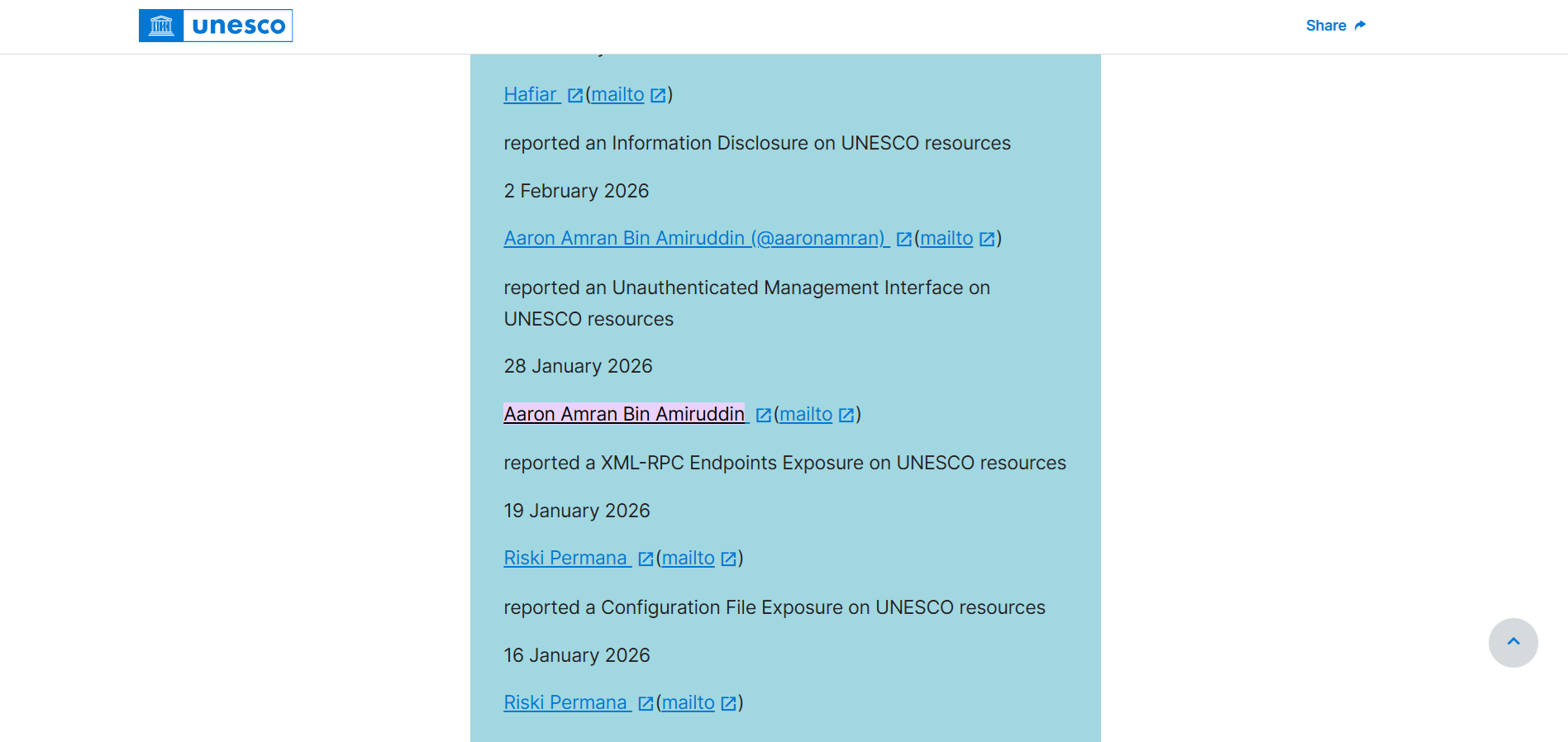
Three days later, on 14 March 2026, UNESCO's Digital Security team updated the Cybersecurity Hall of Fame and I saw my name added into the list.
See you in the next hack.
— @aaronamran
March 2026